ManageiT
An intuitive, easy-to-use management dashboard that
centrally controls all ShieldiT features
centrally controls all ShieldiT features
ManageiT:
Get the big picture
Easily control and manage the security of all your organization’s devices and mobile communication calls, chats and data attachments.
ManageiT integrates with ShieldiT to enable you to control all of the mobile devices and voice and message communications in your network or organization.
Whenever ShieldiT detects a malware infection attempt in one of the network’s devices, ManageiT alerts you, enabling you to take immediate action to mitigate a potential breach.

Voice and conference rooms

Termination (point to multi point communication)

Chats and attachments

CryptoShield activity and threat logs

VPN
Mitigation scales and measure

Encryption key management
ManageiT is an intuitive, easy-to-use management dashboard that centrally controls all ShieldiT features, including:
Voice and conference rooms
PSTN gateway connectivity
Termination
CryptoShield activity and threat logs
Chats and attachments
VPN configuration
Encryption key management
Mitigation actions
PROTECT YOUR BUSINESS


ShieldiT
SECURED CALLS
Secure your entire voice communications


ShieldiT
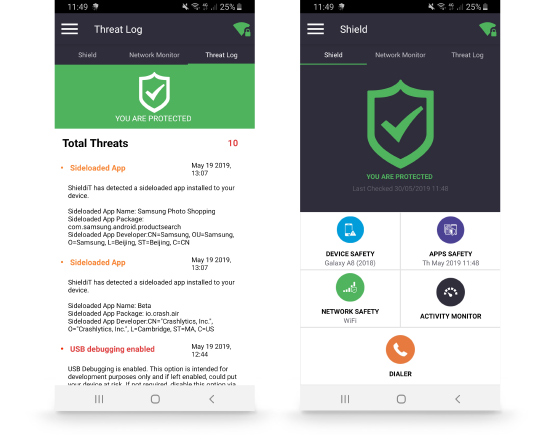
THREAT MANAGEMENT
The IPS that protects your smartphone from host and network threats


ShieldiT
SECURED CHAT
Point to point secured messaging and attachments
